Biometrics: The Foundation of Zero Trust
Joe Ferrigno, Director of Global Safety & Security at Identy.io
The National Security Agency’s Zero Trust Implementation Guidelines (ZIGs) mark a clear shift in how federal agencies operationalize cybersecurity practices. The ZIGs provide next steps for cybersecurity maturity and directly support mission assurance in defense environments. From deployed units to defense industrial base partners, identity compromise disrupts operations and, at its worst, exposes critical intelligence.
Even with these operational guidelines, a significant gap in zero trust architectures persists: high-confidence identity verification. For every defense agency, zero trust is only as strong as its ability to continuously authenticate and verify who someone claims to be.
Phase 1 of the ZIGs focuses on building a secure foundation and understanding of the landscape to enable reliable access decisions down the line. These early stages are critical for implementing identity assurance capabilities that don’t rely on legacy systems like passwords, tokens or access cards, which have become increasingly vulnerable to modern threats and fraud.
Nation-state adversaries and advanced persistent threat groups use stolen credentials, automated phishing campaigns and AI-enabled impersonation techniques to bypass traditional authentication methods and infiltrate defense systems. These tactics increasingly aim to exploit inconsistent authentication across networks to create opportunities for lateral movement. If defense agencies continue to rely on legacy identification methods, their zero trust architecture will remain vulnerable to spoofing and fraud.
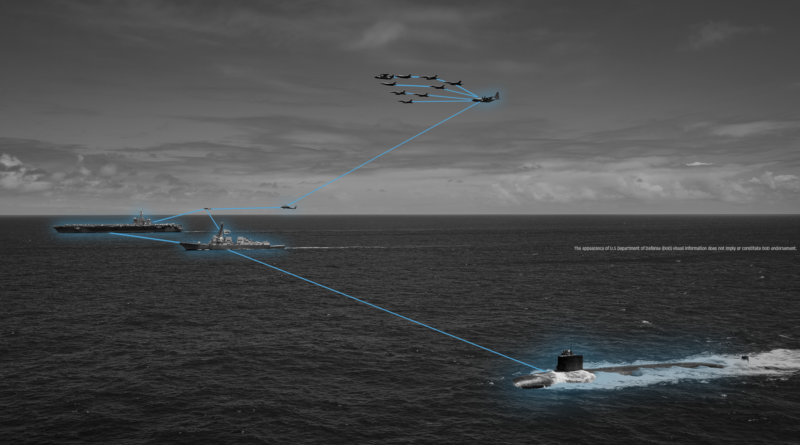
Biometrics strengthen identity protocols by linking access decisions to verified faces, fingerprints or irises rather than reusable or easily forged credentials. This verification extends beyond enterprise IT environments to support secure access in disconnected military operations, equipping warfighters with trusted access at the tactical edge without disrupting workflows.
Implementing identity
For many agencies, the real challenge is implementing zero trust across distributed environments without disrupting mission delivery. Especially in fast-moving defense operations, where even minor issues with authentication or access directly affect personnel safety on the front lines.
The ZIGs provide a broad strategy for zero trust implementation, but success will depend on targeted deployments where identity assurance has the greatest impact. Agencies should start with high-impact areas such as privileged access, sensitive datasets or remote workforce authentication. From there, continuous verification capabilities can be expanded to lower-priority operational workflows.
With technologies such as multimodal biometric platforms, agencies can perform both one-to-one verification and large-scale identification using facial and fingerprint data, reducing manual processes and improving accuracy. Some systems also process data directly on device, reducing dependency on external servers, limiting data exposure and supporting strict zero trust requirements.
A modular, decoupled architecture centralizes access control, equipping agencies with interoperable, high-confidence identity verification across joint environments, where identity extends beyond a single agency or mission partner. Taking a modular approach to zero trust aligns with the ZIGs guidance for agencies to implement capabilities based on current maturity levels and operational constraints, allowing architectures to evolve alongside the threat landscape.
AI-driven biometrics
With the rapid evolution of AI-driven threats, deepfakes, video spoofing and synthetic identities are increasingly being used to bypass traditional verification systems. Modern biometric systems address these threats with active and passive liveness detection and anti-spoofing technologies designed specifically to identify manipulated or fraudulent inputs.
Active liveness tests require users to interact with the system by blinking, smiling or turning their head, adding a challenge-response layer to prove the face is alive. Other systems rely on passive liveness tests that analyze the person’s image for signs of life without requiring any user action. Both capabilities are trained to detect patterns that identify whether a biometric capture is real, preventing adversaries from using synthetic media to impersonate personnel.
The federal government has also recognized the critical need for improved AI threat detection through initiatives such as the Department of Homeland Security’s Remote Identity Verification Rally (DHS RIVR). This program evaluates presentation attack detection against physical attack classes, such as printed images, screen replays, silicone masks and 3D-printed facial replicas, in an independent, controlled environment.
These tests validate the capabilities of biometric tools and provide agencies with the information they need to address security challenges and make more informed, risk-based decisions when selecting solutions for zero-trust frameworks. Identity is the new perimeter, and biometrics, combined with AI-driven liveness detection, play a critical role in continuously validating that a user is who they claim to be.
The federal government has made significant progress in defining what zero trust should look like through initiatives such as the ZIGs and broader defense cybersecurity strategies, including the National Cybersecurity Strategy and DOD Zero Trust Strategy. The next step must prioritize advancing and implementing secure, reliable identity management capabilities.
By focusing efforts on a strong, continuously validated identity, agencies gain an operational advantage in protecting sensitive intelligence and achieving mission success. Biometrics help ensure that every access decision is grounded in accurate identity verification, strengthening zero trust architectures at the point of mission execution.